Oct 03, 2025Ravie LakshmananCybersecurity / Malware A threat actor that’s known to share overlaps with a hacking...
Hacking
Oct 03, 2025Ravie LakshmananVulnerability / IoT Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday...
Oct 02, 2025Ravie LakshmananMalware / Cyber Espionage The threat actor known as Confucius has been attributed to...
Oct 02, 2025Ravie LakshmananRansomware / Threat Intelligence Google Mandiant and Google Threat Intelligence Group (GTIG) have disclosed...
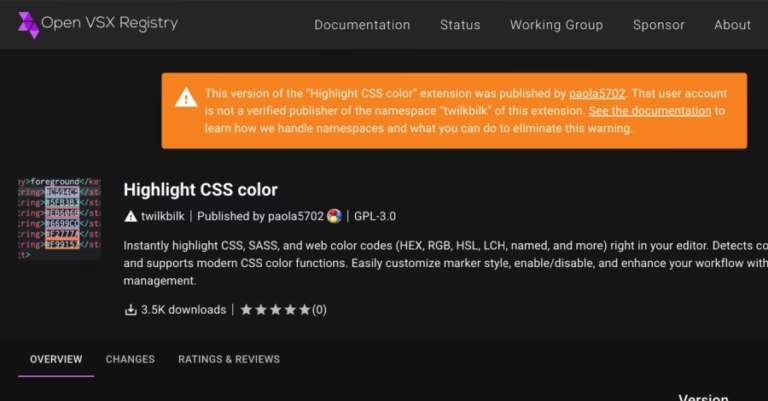
Oct 02, 2025Ravie LakshmananPython / Malware Cybersecurity researchers have flagged a malicious package on the Python Package...
Oct 02, 2025Ravie LakshmananThreat Intelligence / Cyber Attacks From unpatched cars to hijacked clouds, this week’s Threatsday...
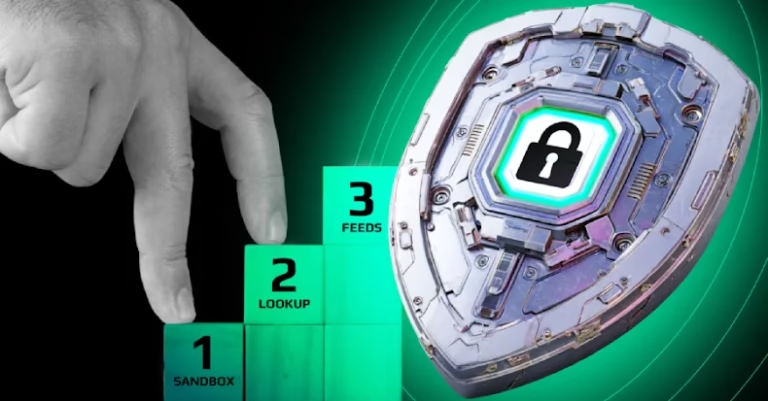
Penetration testing is critical to uncovering real-world security weaknesses. With the shift into continuous testing and validation,...
Running a SOC often feels like drowning in alerts. Every morning, dashboards light up with thousands of...
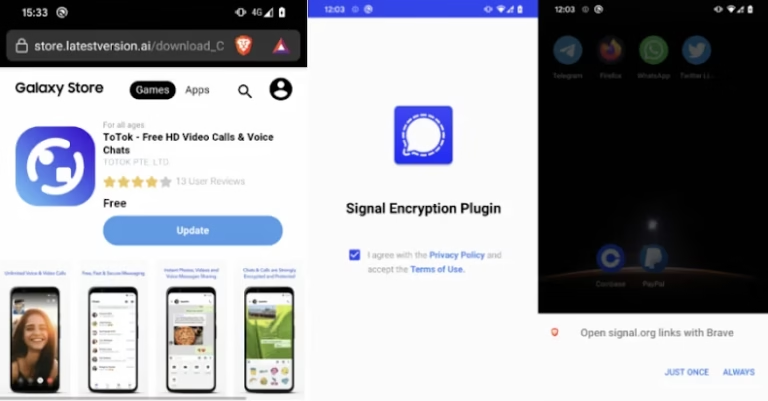
Cybersecurity researchers have discovered two Android spyware campaigns dubbed ProSpy and ToSpy that impersonate apps like Signal...
Researchers uncovered a security flaw in Salesforce’s shiny new Agentforce. The vulnerability, dubbed “ForcedLeak”, let them smuggle...