Are hashtags and reels part of your Instagram marketing? Wondering whether link overlays and early access content...
Month: March 2026
Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are no longer enough to access...
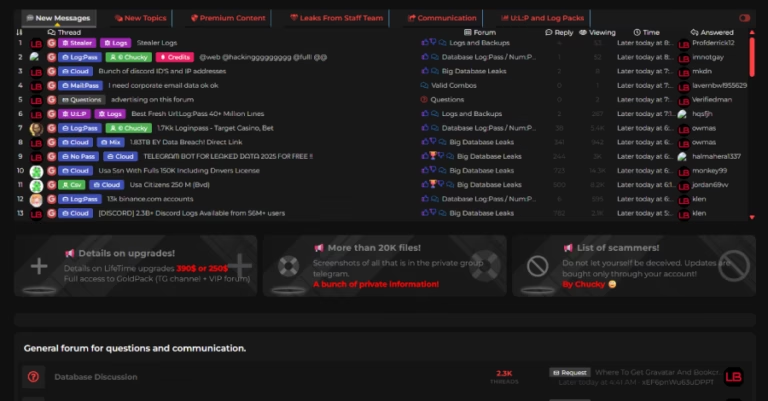
Ravie LakshmananMar 05, 2026Malware / Dark Web A joint law enforcement operation has dismantled LeakBase, one of...
Tycoon 2FA, one of the prominent phishing-as-a-service (PhaaS) toolkits that allowed cybercriminals to stage adversary-in-the-middle (AitM) credential...
When a top cybersecurity firm discovered it had a leak, you would expect the FBI to be...
Cybersecurity researchers have warned of a surge in retaliatory hacktivist activity following the U.S.-Israel coordinated military campaign...
It is a universal moment of stomach-dropping panic: you reach into your pocket or rummage through...
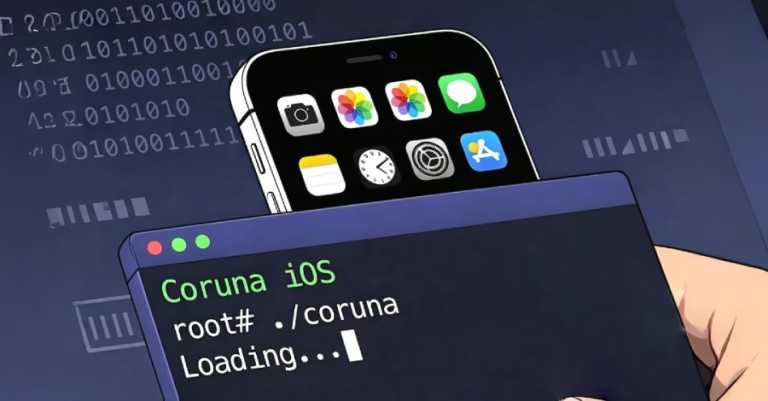
Google said it identified a “new and powerful” exploit kit dubbed Coruna (aka CryptoWaters) targeting Apple iPhone...
The Hacker NewsMar 04, 2026Artificial Intelligence / SaaS Security As AI becomes the central engine for enterprise...
The first few seconds are always the hardest. You step into the water, and your brain...