LinkedIn has been secretly scanning your browser for over 6,000 installed extensions – on every single click...
Year: 2026
Ravie LakshmananApr 08, 2026Cryptomining / Network Security Cybersecurity researchers have flagged a new variant ofmalware called Chaosthat’scapable of hitting misconfigured...
Ravie LakshmananApr 08, 2026IoT Security / Network Security Cybersecurity researchers have lifted the curtain on a stealthy...
Ravie LakshmananApr 08, 2026Vulnerability / Cloud Security The Russian threat actor known as APT28 (aka Forest Blizzard and...
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes...
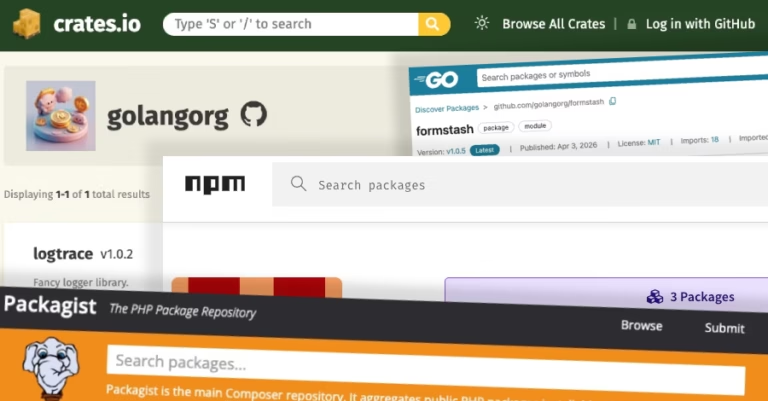
Python Supply-Chain Compromise This is news: A malicious supply chain compromise has been identified in the Python...
Ravie LakshmananApr 08, 2026Artificial Intelligence / Secure Coding Artificial Intelligence (AI) company Anthropic announced a new cybersecurity...
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the...
Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including...
Cybersecurity in the Age of Instant Software AI is rapidly changing how software is written, deployed, and...