In a birth injury case, the collection of evidence is crucial for establishing liability and demonstrating...
Year: 2026
Gathering evidence is a critical component in the aftermath of an accident, serving as the foundation...
A long-term and ongoing campaign attributed to a China-nexus threat actor has embedded itself in telecom networks...
Ravie LakshmananMar 26, 2026Cybersecurity / Hacking News Some weeks in security feel loud. This one feels sneaky....
Unmasking impostors is something the art world has faced for decades, and there are valuable lessons from...
Ravie LakshmananMar 26, 2026Browser Security / Vulnerability Cybersecurity researchers have disclosed a vulnerability in Anthropic’s Claude Google...
The Hacker NewsMar 26, 2026Security Testing / Security Automation Most teams have security tools in place. Alerts...
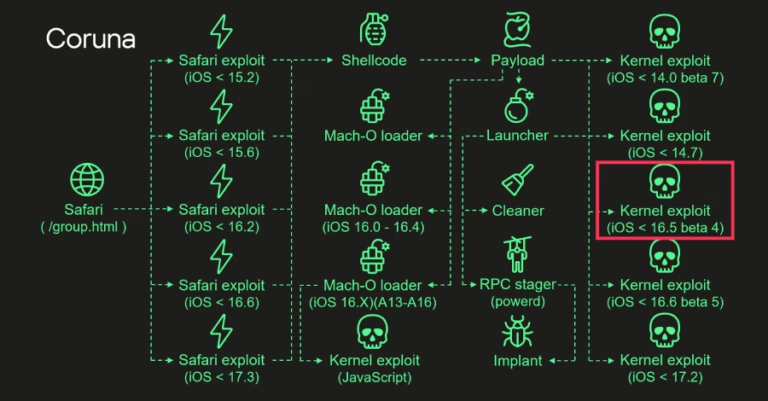
Ravie LakshmananMar 26, 2026Malware / Mobile Security The kernel exploit for two security vulnerabilities used in the...
A disgruntled data analyst decides that the best response to losing his contract is to steal the...
Social Marketing Trends
The data you’ve been missing!
Need a new plan? Discover how...